In ensuring secure access to sensitive client data, the insurance industry encounters distinct challenges in protecting data against an increasingly sophisticated cyber threat risk landscape.
For example, gone are the days when employees worked five days in the office, the next generation of cat modelers and underwriters want the freedom to work where they want. As a result, companies need to support hybrid work environments, but they must also ensure the security of their data. This presents a challenge for organizations to balance security and productivity.
With over 350 clients currently utilizing Moody’s Intelligent Risk Platform™ (IRP), and many integrating Data Bridge™ to construct their T-SQL workflows, there is a growing need to develop solutions that address a wider range of client requirements while prioritizing security compliance.
Although Data Bridge already allows T-SQL connectivity by updating firewall rules and has been a successful and widely accepted solution, there has also been tremendous interest in a more stringent solution that aligns with customers’ increasingly strict organizational security policies.
To help protect your data and privacy, a VPN, or Virtual Private Network, is a service that provides a secure connection while giving you greater freedom to access content from around the world.
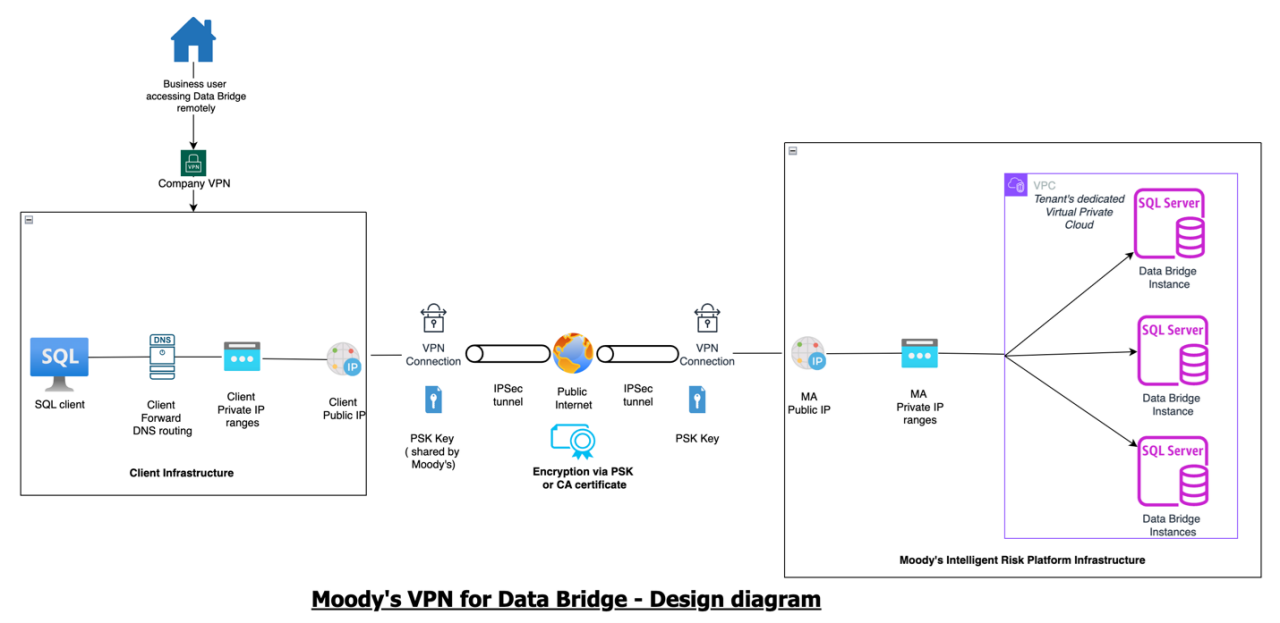
This year, we will launch Moody’s VPN for Data Bridge on Moody’s Intelligent Risk Platform. This feature enables customers to establish VPN connectivity to Data Bridge instances on their tenant with advanced encryption, ensuring secure T-SQL connectivity.
The solution
The Moody’s VPN for Data Bridge establishes a secure and encrypted connection over less secure networks, such as the Internet. It extends your organization's private network across a public network (such as home office, airport, or coffee shop Wi-Fi), enabling users to connect to the Data Bridge SQL instances running on Moody’s cloud infrastructure as if they were accessing local network resources.
This solution also ensures compliance with a critical aspect of secured connectivity, i.e. business users must always be connected to the company’s VPN to establish connectivity to safeguard the confidentiality and integrity of the information being transferred.
How Moody’s VPN for Data Bridge elevates data security
A site-to-site VPN is a specific VPN deployment designed to connect two organizational networks. It is crucial for businesses that require secure, reliable connections between separate networks over the Internet.
With Moody's VPN for Data Bridge, businesses can achieve site-to-site VPN connectivity to Data Bridge instances via the company's main network. It forms a secure, encrypted tunnel between Moody’s infrastructure and a user’s organizational network over the Internet, to provide T-SQL connectivity and allow secure communication and data transfer between these two networks.
Utilizing Moody's VPN for Data Bridge also enhances the organization's operational efficiencies:
- Single secure connection for all users: With one click to connect to the organization’s VPN, business users can seamlessly access Data Bridge instances and begin their work efficiently. Users no longer need to be concerned about getting firewall rules updated every time the assigned IP address of the user machine changes.
- IT support process streamlined: Business users no longer have to raise general support requests when traveling or working from a new location. Once the VPN connectivity is successfully established between Moody’s and the client’s organization, user connectivity will be seamless with Data Bridge. This would reduce the total operational cost immensely for the client IT teams.
Internet Protocol Security, commonly known as IPSec, stands out as an essential protocol within the security design realm. A suite of protocols designed to ensure the integrity, confidentiality, and authenticity of data communications over an IP network, IPSec operates at the network layer and is widely used to secure VPNs and other internet communications.
Moody's VPN for Data Bridge takes further advantage of the IPSec protocols, specifically the Internet Key Exchange (IKE) protocol used to set up a Security Association (SA) by negotiating encryption and authentication keys between two IPSec peers. It ensures that both parties can securely share the necessary cryptographic keys.
The ‘Tunnel Mode’ of the IPSec protocol encrypts and authenticates the entire IP packet, encapsulating it into a new packet with a fresh IP header.
Key security features:
- Protocol and Layer: IPSec protocol operates at the network layer (Layer 3) of the OSI model, hence, it provides secure communication by encrypting IP packets between the client user machine and the Data Bridge instance hosted on Moody’s infrastructure.
- Confidentiality: Creating a secure ‘tunnel’ between two sites ensures that sensitive information such as policy details, customer personal information, and claim records, remains confidential.
- Encryption: All T-SQL data transferred between the SQL client of the business user and Moody’s infrastructure is encrypted using strong encryption protocols such as IPSec to secure data as it travels over the public Internet.
Ensuring adherence to organizational compliance requirements
Securing data transmission using Moody’s VPN for Data Bridge helps insurers meet the latest data protection and privacy regulatory requirements.
- Data protection laws: Insurance companies are subject to various data protection regulations, such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) of 2018 in the United States, and other regional laws. These regulations require companies to implement measures to protect personal data and ensure its confidentiality and integrity.
- Secure communication channels: By using Moody’s VPN for Data Bridge, insurers can showcase their implementation of secure communication channels as part of a compliance strategy. This can be crucial during audits or in the event of data breaches, as it shows a proactive approach to data protection.
- Controlled access: This feature allows companies to control access to their data over public networks, as only authorized devices and users can connect, and access can be restricted based on roles and responsibilities. This helps maintain compliance with the principle of least privilege.
- Audit trails: Users can view logs and monitor connections to keep records of connections and access attempts. These logs are valuable for auditing purposes and can help security teams detect unusual or unauthorized activities that might indicate a security breach or malicious behavior.
In conclusion, Moody’s VPN for Data Bridge further amplifies the Intelligent Risk Platform benefits providing a unified and secure infrastructure that supports connectivity to cloud-based Moody’s Data Bridge.
By adopting Moody’s VPN for Data Bridge, insurers can build a robust and secure network foundation that safeguards their critical data and supports operational needs, to position their business for future growth and innovation.
For additional details regarding the forthcoming innovative data security features within Moody’s Intelligent Risk Platform, please reach us at sales@rms.com.
LEARN MORE
Moody's insurance solutions
Our differentiated solutions bring together technology, data and analytics and insights, helping insurers, reinsurers, and brokers address their most complex challenges and make better decisions with confidence – therefore helping to close the insurance gap and drive performance.

